 Given our previous opposition to various legislative proposals aimed at the Internet such as our take on SOPA, the short lived Verisign Takedown Proposal, we would be remiss if we did not comment on Bill C-30, “Lawful Access”. I read it a couple nights ago and I think it’s one of the worst legislative proposals ever tabled in, what I think is quite frankly, an effort to “keep a lid” on the internet.
Given our previous opposition to various legislative proposals aimed at the Internet such as our take on SOPA, the short lived Verisign Takedown Proposal, we would be remiss if we did not comment on Bill C-30, “Lawful Access”. I read it a couple nights ago and I think it’s one of the worst legislative proposals ever tabled in, what I think is quite frankly, an effort to “keep a lid” on the internet.
When I read SOPA, and PIPA I had a textdoc open to which I cut-and-pasted various sections of note, in each case I had maybe a half dozen passages which I tagged with brief comments such as “troubling”, “overly broad” or “slippery slope”.
When I finished reading C-30 I had 23 sections of notes, with comments like “wtf?”, “surely, they jest”, and “omfg”. It is nothing less than a framework to enable unfettered state access into all domestic network communications (except for banks, who are exempt), total unwavering compliance from all internet providers, and penalties for non-compliance which seem to occur without due process.
Yesterday the news out of Ottawa was that the government was possibly stepping back from the proposal in its current form and sending it to Committee for revisions. But as Michael Geist notes, the battle seems to be playing out over what getting warrantless access to “subscriber information” actually entails. The government says its no worse than publicly disclosed details in a phone book, privacy advocates beg to differ.
To me it’s all a sideshow. Regardless of what subscriber details are given to authorities, there are numerous other provisions in the Bill which make it nothing less than chilling:
- If a service provider provides encryption capabilities, they must reserve the capability to provide unencrypted intercepts to authorities (but they do not need to do this if the communications are already encrypted when they transit their networks)
- “Enable interception of communications generated by or transmitted through the apparatus to or from any temporary or per-manent user of the service provider’s telecommunications services”
- Provide the ability to correlate “all elements of intercepted communications” – what this means to me is that if an access provider has been ordered to furnish data on you (including your IP), they have to be able to to give correlated data for that IP: everywhere you’ve visited or connected with over the network, which protocols, and I am assuming in the case of an access provider, the contents of those communications.
- Facilitate simultaneous intercepts from multiple agencies.
- Any new software or hardware installed by any service provider must meet the “operational requirements” of the act “even if the form of the software in question would require the telecommunications service provider to acquire additional software licences or telecommunications facilities to achieve that increased ability“.
And, just in case any of this is too onerous on service providers, the Minister is happy to help out:
The Minister may provide the telecommunications service provider with any equipment or other thing that the Minister considers the service provider needs to comply with an order made under this section.
Oh, and by the way, the Minister may also compensate service providers for additional expenses incurred in becoming compliant with the act, or pay for said equipment it furnishes to the service providers. In other words, it all gets paid for out of our taxes.
The compliance requirements for all service providers is nothing less than nightmarish:
- All providers must permit police officer, RCMP or CSIS officer the ability to assess or test the service providers facilities that may be used to intercept communications.
- Service providers to provide lists of names of employees who would be tasked with undertaking intercepts, who may then be subject to police background checks
- Section 34(1) – “An inspector may, for a purpose related to verifying compliance with this Act, en-ter any place owned by, or under the control of, any telecommunications service provider in which the inspector has reasonable grounds to believe there is any document, information, transmission apparatus, telecommunications facility or any other thing to which this Act applies.
Once in the facility, said inspector can:
- “examine any document, information or thing found in the place and open or cause to be opened any container or other thing;”
- “examine or test or cause to be tested any telecommunications facility or transmission apparatus or related equipment found in the place;”
- ” use, or cause to be used, any computer system in the place to search and examine any information contained in or available to the system;”
- make copies of anything they want.
Then there is the extra-judicial provisions for non-compliance by any service provider:
39. Every person who contravenes a provi-sion, order, requirement or condition designat- ed under subparagraph 64(1)(p)(i) commits a violation and is liable to an administrative mon- etary penalty not exceeding the prescribed maximum or, if no maximum has been pre- scribed, to a penalty not exceeding $50,000, in the case of an individual, and $250,000, in any other case.
This happens, not by being charged with an offense, not by being summoned, but by being served a “Notice Of Violation”.
41. (1) A designated person may issue a notice of violation and cause it to be served on a person if they believe on reasonable grounds that the person has committed a violation.
42. (1) A person who is served with a notice of violation must, in accordance with the notice, pay the penalty set out in the notice or make representations with respect to the amount of the penalty or the acts or omissions that constitute the alleged violation.
(2) A person is deemed to have committed the violation if they either pay the penalty in accordance with the notice of violation or do not pay the penalty and do not make representations in accordance with the notice of violation.
Also, an employer is liable for a “violation” if it is committed by an employee, whether or not the employee is identified or proceeded against.
And to top it all off, as a final “fsck you” from the Minister to all Internet Service Providers in Canada:
All ISPs must, within 6 months of the Act becoming law submit a report to the Minister of Public Safety and Emergency Preparedness detailing the facilities they operate.
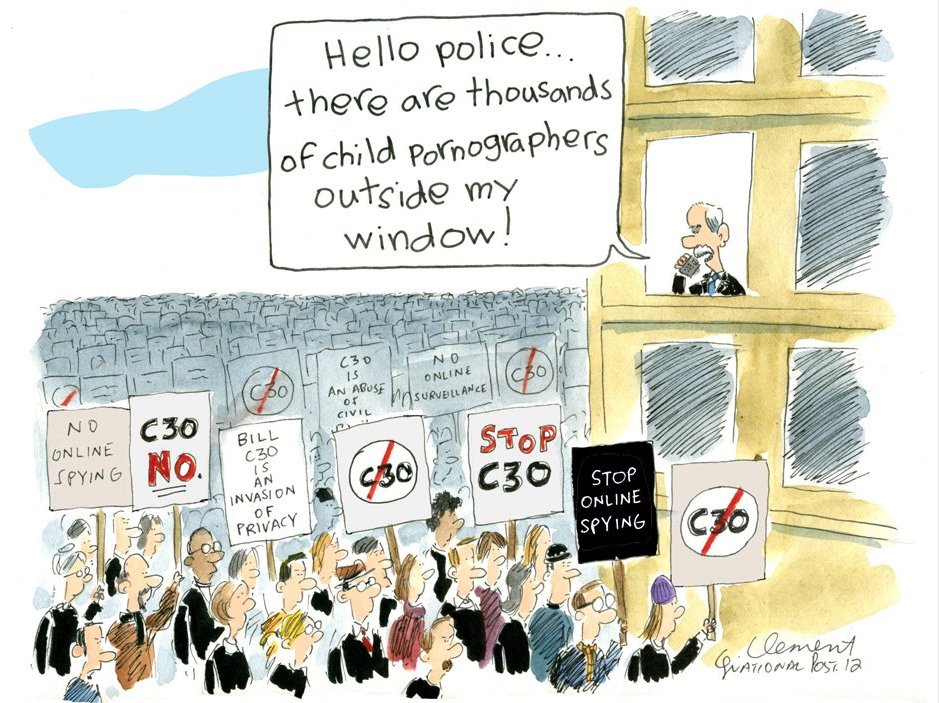
But hey, if we don’t like it, then according to Safety Minister Vic Toews “we must be siding with the child pornographers“, right?
What This Law Will Do If Passed
So basically what happens if this becomes law is this:
- Canadian service providers will lose business to foreign technology providers who are not constrained by warrantless state oversight into their facilities, customer information and data.
- Service Providers will pass along indirect costs of compliance to customers since there will inevitably be additional expenses outside the scope of government reimbursement.
- Kiss good-bye what I think is currently a fairly healthy climate of willful, uncoerced co-operation between ISPs and Law Enforcement. ISPs now have their own Acceptable Use Policies and tend to self-police in ways that help LEA when actual crimes are being committed. Existing law works and as Michael Geist notes in another post, gets results. Bring in this law, and law enforcement becomes Big Brother. Nobody wants to deal with Big Brother.
- A technology Brain Drain will occur. If this law comes through looking like this then I for one will start my next company somewhere else. I doubt I’ll be alone in that. Crappy winters are one thing, but this, I don’t need.
- Not a single technology entrepreneur, investor, executive or knowledge worker in Canada will vote for the Conservative Party ever again. Maybe that’s not a bad thing.


Do we next allow the police to randomly walk into our homes and search without a warrant? I have some right to privacy, some right to not have all of my Internet communications analyzed, and interpreted perhaps out of context.
Do I have something to hide? No, I don’t, but I don’t expect this means I have to relinquish my rights to privacy. We HAVE a working system. Think I’m a bad guy…tell it to the judge, get a warrant. Of course we all want child pornography stopped… don’t use that against those of us who value privacy.
Sections 41&42(1,2)look like big money makers for these CONthugs. No wonder there in such a desperate hurry to pass this insanely intrusive bill. #cdnpoli #billc30
“Not a single technology entrepreneur, investor, executive or knowledge worker in Canada will vote for the Conservative Party ever again. Maybe that’s not a bad thing.”
I don’t think the current reincarnation of the Republican party north gives a rats ass about that demographic, since it doesn’t benefit their base (aka oil companies and the 45+ baby boomers that voted them into power.
I’m no fan of the Liberal party, but at least they usually stopped the stupid train the BS train and blatant croynism and corruption. This version of the Conservative party has blown right through that station and is following in the repetitive (and extremely short sightedness) of it’s predecessors in aiming to destroy a growing section of the economy. Whether it’s Deifenbaker in killing off aerospace, Mulroney in killing off manufacturing and retail, or Harper in killing off the IT market, having the Cons in power is just not good for businesses in a growing market segment. Kind of pathetic for a party that’s supposedly representing Canadians.
Great piece. As a tech worker I am particularly enraged by section 34 of this bill, and the new obligations it intends to enforce. Compulsion, coercion and costs to providers are the only things protected by this bill.
Actually, it’s even worse than all this. The one thing missed is the nature of these “inspectors” and under what circumstances they can do this. The answer is, anyone the minister designates is an inspector, and they don’t have to have any reason at all. So it’s not just the police, it could be, say, an employee of a public relations firm helping the Conservative party’s election campaign, or someone working for a pipeline company. And not only do they not have to have a warrant, they don’t have to be investigating a crime or doing anything in particular, nor do they have to tell anyone what information they’re looking for or why. So that PR firm could be grabbing all the emails from a rival PR firm working for the Liberals or NDP, the pipeline employee could be on a fishing expedition for dirt on Greenpeace members opposing their pipeline, and it would all be completely legal as long as the minister decided they were “inspectors”.
Fun, huh?
I think the real fail of this bill is going to be the definition of ‘Service Provider’ and all the exemptions there-in.
If Starbucks (public libraries, universities or any other place that provides relatively anonymous access) is exempt, then the whole act is fairly pointless. and obviously so.
Re-jigging it so that Starbucks (libraries, etc) will be required to maintain records of who was active on what IP at a given time, will be too onerous, and the corporate world will shut it down.
Good blog. better the the CBC article. 🙂 The content is certinly disheartening, but we are not alone in this. australia already has a small amount of intyerent censorship, while Britian has already passed the equilivalent of SOPA. To be honest I feel like no matter who the people vote for we still get skrewed…
What can people do locally against Bill C-30? can they pass local legislation nullifying the law if it comes into effect in our area?
regards,
andrew
Twice as worst as the patriot act. Harper = new world order big brother uncontested after his re-election. I never voted for him.
This is total bull. Completely a violation of privacy. There is no need for anyone to be viewing what the mass poopulation is doing, chats, messages, without a proper document. That is the purpose of getting warrant! Its disgusting to even consider this and I for one would see it happen over my own cold dead body. They have no rite to invade peoples privacy because they have suspicions of someone. Ive been pulled over before by the cops I’ve heard their excuses for why they do it, whats to stop them from being like yea your a suspect were gunna have to look into your personal info online. Bull. If you cant find proper documentation of someone breaking the law thats your fault for lacking at your job does noot mean you should violate the given right of every Canadian jus to make your job easier. You get ppaid to do your job, so do it, dont take from us what little we have. This new bill is a joke, who gives the government the rite to snoop into any individuals life. The fact that they have the open ability to do so, monitor such, is bull. If this passes, you will never hear the end of it. I promise you that with my last breath.
This bill needs to be passed. I have research this bill extremely thoroughly and what I see is the bill is greatly misunderstood, people are taking section 17 as the whole bill and ignoring the rest. Section 17 of the bill is the part the outlines the exceptions, this is where is allows any police officer to go through internet bill-when an emergency has or is taking place. Otherwise only specific officials, a number as few as 6, can go through bills. Additionally what I see and know is the bill needs to go through because the police system cannot keep up with the internet and the advantages it gives to organised crime and other illegal groups and people committing crimes. An example of how important that this bill goes through is the Tori Stafford case, on Michael Rafferty’s computer were Google searches and other evidence that would clearly show that he committed the horrible things that he did- but they could not access his computer with this bill in place. The ruling would have gone much faster if they did and sad to say it but there are more people like him out there in Canada, but if this bill does not go through than they can continue to commit the crimes they do. So unless you want to let these things happen than please tell other people what I just did to you.
The police cannot and will not go through your internet unless you have committed crimes or are suspected of committing crimes.
Unless you are wanted for committing crimes than there is absolutely no reason you shouldn’t want the bill to go through.
THE MAN IS NOT WATCHING YOU- get a hold of yourself, your not that important. Stop being self conceded and think of Tori Stafford and other kids who are put in danger every second this bill isn’t in place.
I find your arguments circular and inconsistent. On one hand you say that organized crime is ahead of the law, but the example you give is of the Tori Stafford case. I don’t believe it needs to be pointed out that as heinous as that crime was, it had nothing to do with organized crime. Further, this law would not prevent this type of crime from occurring and the perpetrator was arrested and convicted without the law existing. Both his cell phone and internet histories were used in evidence and it was all obtained within the existing legal framework.
The argument “you only have to worry about it if you are committing crimes” gets really dicey when you tack on the “…or are suspected of committing crimes” – because at the end of the day everybody is suspect. Just have a look at what’s happening south of the border with the TSA, where all reason has gone out the window and literally everybody is being treated as a “terrorist suspect”.
The burden on ISPs is insane. Section 34 enables “inspectors” (who may not even be officers of law enforcement agencies) to enter any ISP premise and examine anything simply to verify “compliance” with the act.
YOU NEED A WARRANT- EXCEPT FOR SECTION 17. SO Jayson YOU ARE WRONG
C-30 is known as the “Protecting Children from Internet Predators Act.” Interestingly, neither are mentioned in the bill itself. Vic Toews once said “… you’re either with us, or the child pr0nographers.”
Well, the enemy of my enemy is my friend, so I think I’ll stand with the pr0nographers for the point of eliminating the enemy.
Look.. To the people who would like to sign away their right to privacy.. Go ahead. I won’t because I like mine. Thanks
Hey Bub,
As you can see, the bill didn’t pass, so it looks like the Internet spoke and was heard.
http://en.wikipedia.org/wiki/Protecting_Children_from_Internet_Predators_Act#Progression_of_bill